Abstract
The global reach of the Internet and its everyday use have allocated the responsibility for its security among a wide range of the WWW users. The Internet does not only provide access to the world information but also allows its users to construct their own worlds. The Internet environment makes a more individual cognition of the world around possible thanks to which the transformation of the very structure of communication experience occurs. A gap between the true / real “self” and false / ideal “self” can lead to psychological vulnerability and poorer psychological security of the individual. The insight into the substance and the reciprocal relationship between “real self” and “online self”, the examination of the given representations in the context of security pose a pressing task whose is much sought-after by contemporary social practices. The study showed differences in the degree of perceived security in real-time and online interaction. Some distance of the “Online self” from categories “danger” and “security” in the adolescents’ consciousness is observed. The category “Online self” in the teenagers’ consciousness goes beyond the criteria of gangers and safety of real life, which represents certain threats to psychological security especially given teens’ inadequate digital competence and personal immaturity.
Keywords: Adolescentspsychological securitythe Internet environment
Introduction
Technological strides in various areas of human activities have resulted in different ways of joint work and have transformed communications and social ties. And the Internet has had a special role to play in revolutionizing communication and search for information. On the one hand, it provides users with new opportunities to develop and express themselves, on the other, it bears new risks and threats. The internet simultaneously has equipped its users with tremendous capabilities and confronted them with numerous risks associated with continuous focus on security.
The Internet environment makes a more individual cognition of the world around possible thanks to which the transformation of the very structure of communication experience residing in the construction of one’s partner image and rules for interacting with him occurs. Thus, new technologies provoke a new content. “As the case stands, the internet penetrates all the multi-dimensional social space and represents an absolutely different (in its meaning and quality) facet where various social fields meet. The world witnesses that manifold human activities interfuse, the internet technologies have made their presence felt in every sphere of our life, be it economy, society, culture, politics, education, as well as everyday life and leisure” (Zotova & Zinchenko, 2014, p. 61).
Over 26 million children live in Russia, which makes up approximately 23.3% of the county population. Children are a crucial and the most valuable asset for the development and socio-economic growth of the country, and in this respect the formation of psychological security in children and adolescents as “a state of personality when the individual can satisfy his/her basic needs for self-preservation and be aware of his/her own (psychological) security in a socium” (Zotova, 2012, p. 89) acquires relevance to the contemporary world. Arguably, we deal with social demand for research on children and adolescents’ psychological security as it can become central for prognostic understanding of the Internet users’ behavior and its consequences.
Since the advent of the Internet psychologists have been exploring its role in mental health of adults and children (Aboujaoude & Starcevic, 2014; Greenfield & Yan, 2006; Shapira et al., 2003; Yen et al., 2007; Young, 1998). The average time for online surfing of 12-16s’ majority is 6-12 hours a day (Dontsov & Perelygina, 2014, p. 137). These findings have shown that online games cause addiction, negatively influence children’s life (take away from school life, communication with friends and family), which can lead to distress and loneliness (Livingstone & Haddon, 2009; Shapira et al., 2000). Extensive research on the linkage between the time spent online and mental disorders including depression, attention deficit hyperactivity disorder and suicidal behavior (Blachnio et al., 2015; Do et al., 2013; Ha et al., 2007; Kim et al., 2006; Tsitsika et al., 2011; Yoo et al., 2004) have been carried out. However, the cause-and-effect relationship has not been confirmed yet: mental disorders provoke the Internet overuse, or vice versa (Davis, 2001; Dong et al., 2011; Green et al., 2011; Lam et al., 2009; Morrison & Gore, 2010;Morahan-Martin et al., 1999; Mitchell, 2000), which is often described as the Internet paradox (Kraut et al., 1998).
Whether the Internet offsets psychological stress or, on the contrary, the Internet gives rise to it is still a matter of debates. And the results of numerous studies are controversial. So, it was found that introverts who often use the Internet demonstrate a lower self-esteem and a higher level of loneliness (Kraut et al., 2002). Other investigations, in contrast, provided evidence that the unregulated use of the Internet mitigates symptoms of loneliness (Kim et al., 2009; Pratarelli et al., 1999).
Facebook has enormously increased the number of its active users for the last decade and its number is growing every year (Internet World Stats, 2017). Every user spends, on average, about 14 minutes a day, which constitutes 16.6% of total online time (Comscore, 2011). Networking sites offer its members utilitarian and social advantages. Facebook, in the first place, provides its users with capabilities to interact with different people called “Facebook friends”. Thanks to it, users especially those with low self-esteem and low life satisfaction can improve their psychological wellbeing (Ellison, 2007). However, multiple online activities can result in an excessive amount of time on the Internet and Internet addiction (Turel & Serenko, 2012; Turel, 2014), which is more relevant to people with low self-esteem, low self-efficiency and certain psychological traits (Brand et al., 2014).
The use of social networking sites can facilitate a false self-image (Rogers, 1954; Winnicott, 1960), which lowers the level of wellbeing and causes different psychological pathologies. Unlike other online activities such as portals, news web-sites and even blogs where comments can be anonymous or under fake names, social networks sites require quite definite self-identification not only in terms of names but also in terms of friends, actions, photos, feeling and preferences. As a result, some users consciously or unconsciously make a decision to modify their personality.
A false self-representation, to some degree, is far from being a discovery of the digital era. A gap between “the real self” and “the ideal self” is called a mismatch (Rogers, 1954) and can lead to the creation of the “false self” (Winnicott, 1960) overshadowing “the real self”. Both authors C. R. Rogers and D. W. Winnicott supposed that a low degree of deception is possible and, probably, is not harmful. However, high degrees of deception, or in other words, larger distances between “the true/real self” and “the false/ideal self” can result in unstable psychological functioning, psychological vulnerability and lower psychological security of the subject.
The study into laws and regularities of psychological security formation of children and adolescents on the Internet is of prognostic character. It is known that psychological security is a factor enhancing high IQ (Paterson et al., 2002), impacting self-respect (Little & Kobak, 2003), social competence (Helson & Wink, 1987), empathy (Van der Mark et al., 2002), cooperation (Scheider, 2001), confidence (Edmondson & Mogelof, 2006), manifestations of creativity (Urban, 2003), activeness (Tegano, 1990). As it is during childhood and adolescence that the formation of psychological security takes place, any formative and corrective actions aimed at creating and developing psychological security will be the most effective.
The global reach of the Internet and its everyday use have allocated the responsibility for its security among a wide range of the WWW users. The Internet does not only provide access to the world information but also allows its users to construct their own worlds. However, vast research efforts focused on the Internet spread have not considered such aspects as views, values with regard to psychological security and factors defining the Internet users’ behavior.
Problem Statement
The insight into the substance and the reciprocal relationship between the “real self” and the “online self”, the examination of the given representations in the context of security pose a pressing task the solution of which is much sought-after by contemporary social practices.
Research Questions
The implementation of the study involved the following issues to be addressed:
To reveal differences in the perceived security in the course of the teenagers’.
To identify specific features of the perceptions of personality in the Internet environment.
Purpose of the Study
To explore the characteristics of psychological security exhibited by the adolescents in the Web space.
Research Methods
The sampling selected in line with the study’ goal consisted of the group of teenagers from the Sverdlovsk region. The group involved 147 schoolers from comprehensive schools aged 14-15 (average age 14.69), which corresponds to the G. Craig’ periodization of adolescence (Craig & Baucum, 2001). There were 79 females and 68 males in this group.
To realize the objective set the semantic differential method for researching the constructs of consciousness was used. We chose Peabody methodology which he labeled “4-pole model of personality traits” modified by Shmelyov (2002) as our instrument. The objects of assessment were the following states: “the current self, “the past self”, the secure self” and “the self in danger”.
The results obtained were analyzed with the help of multidimensional scaling ALSCAL, Wilcoxon t-test and exploratory factor analysis. The data were processed and analyzed via SPSS 20.0.
Findings
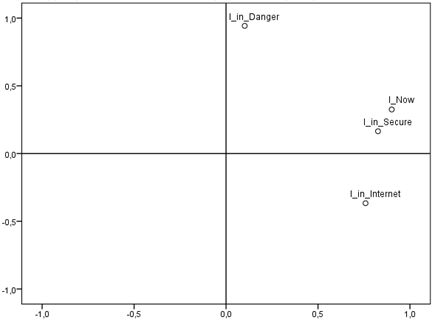
The application of multidimensional scaling allowed us to construct a diagram reflecting mutual arrangement of the following categories “the current self, “the self in danger”, “the secure self” and “the online self” in adolescents’ consciousness.
The state “the current self” relates to a greater extent to the state “the secure self” – the distance between these categories is minimal – than to the state “the self in danger”. The category “the online self” of the teenagers is not only distanced from their representations of being secure but also from their “real self” (figure
The assessment of semantic distances between the objects of semantic differential allowed us to clarify numerical values of distances of the categories under consideration in the teenagers’ consciousness (table
One can note that in the respondents’ consciousness “the current self” and “the secure self” are closer in the semantic space than the categories “the online self” and “the secure self’. And the teenagers see danger as a kind of being closer to real life than to virtual reality.
In order to examine foundations according to which the teenagers allocate the categories in question in their consciousness the factor analysis was carried out resulting in identifying 5 significant factors (table
The obtained factor structure matches personal factors of the Big Five with the exclusion of the last factor: in the structure obtained instead of the factor “Emotional stability” the factor “Flexibility” (a factor with maximum load by the scale “Flexible-Inflexible”) was singled out. It is worth mentioning that the above table lists the variables with maximum load in each factor.
The data material obtained was further restructured in accordance with the identified personal factors, and the comparative analysis of the intensity of each factor (on the basis of the variables taken into consideration) in the categories “the current self” and “the online self” was conducted (table
Therefore, significant differences in the adolescents’ representations of “the current self” and “the online” self” can be noted. On the Web teenagers are likely to consider their “self” to be more self-confident, flexible, and intelligent but less-controlled than “the current self” in a real situation.
The given study has shown differences in the degree of perceived security in real-time and online interaction maintained by teenagers.
For the most part, some distance of the “online self” from categories “danger” and “security” in the adolescents’ consciousness is observed. In other words, the state “the current self” is characterized by a close distance to “the secure self” and to the state “the self in danger” as well. Thus, the category “Online self” in the teenagers’ consciousness goes beyond the criteria of gangers and safety of real life, which represents certain threats to psychological security especially given adolescents’ inadequate digital competence and personal immaturity.
In the course of the study it has been revealed that the construction of the “self” in situations “the online self” and “the current self” is based on the universal global personal factors of the Big Five which are sustainably reproduced on all kinds of material. In addition, statistically significant differences in four out of five factors of the representations considered – “the current self” and “the online self” ere revealed, which suggests evidence for the “multiple self” of modern adolescents.
Teenagers on the Internet under-assess their behavior self-control at a statistically significant level, which speaks about a greater light-mindedness, a penchant for reckless actions and impulsiveness in virtual space. They make fewer efforts to meet socially accepted requirements and cultural norms, which is partly associated with anonymity while using the Web. Our results are consistent with the findings of English psychologists, who stated that “impulsiveness is a personality trait that reflects an urge to act spontaneously without thinking or planning ahead for the consequences of your actions” (Coutlee et al., 2014, p. 2) and negatively correlates with secure behavior, making it possible to predict risky behavior online.
Besides, the perception of ‘the online self’ should be indicated as being more active and confident compared to ‘the current self’. Thus, teenagers online are likely to be more sociable, relaxed, carefree, and optimistic. Thus, Uebelacker and Quiel (2014) fixed a direct linkage between the traits of the Big Five (John & Srivastava, 1999) and susceptibility to manipulation on the Internet. The authors established in their study that people exhibiting such traits as fairness, extraversion, openness to experience, and consent often appear to be involved in problems of cyber bullying, cyber terrorism, becoming victims of fraud.
The insights into specific features of the personality representations online and psychological security on the Web can be effective instruments for understanding reasons for secure/insecure behavior on the Internet. Moreover, the identification of interrelationships between psychological characteristics and the nature of psychological security can be used for designing methods to assess cyber security on a whole.
The results of the study can act as a basis for qualitative assessments of risks emerging upon the teenagers’ involvement in the Internet environment not only on the part of technologies but also due to human factor.
Conclusion
The relevance of the study resides in the prospects for results to be gained in studying cyber security in the socio-psychological context. Research on individual predictors of psychological security on the Internet can enhance understanding of the causes of secure/insecure behavior online, and the establishment of the relationship between socio-psychological characteristics of the users and the nature of psychological security can be used to design techniques for assessing cyber security on a whole.
The identification of people with a high level of cyber security will help define socio-psychological factors that shape a specific “secure” mindset and behavior.
The treatment of psychological security as an effective therapeutic strategy is of scientific value. Such a strategy implies that the absence of the state of security contributes to personality vulnerability, and that a way to recovery is not only limited to easing the negative symptoms but also resides in improving psychological security of children and teenagers, which, in its turn, increases individual resilience and forms a buffer against life stresses.
The results of the study can become a basis to model and strategically plan a level of psychological security, to bridge the digital gap of users, to qualitatively assess both technological and human-factor risks
Acknowledgments
The article was supported with a grant from the Russian Science Foundation (project № 16-18-00032-П).
References
- Aboujaoude, E., & Starcevic, V. (2014). Mental health in the digital age: grave dangers, great promise. Oxford University Press.
- Blachnio, A., Przepiorka, A., & Pantic, I. (2015). Internet use, Facebook intrusion, and depression: results of a cross-sectional study. Eur. Psychiat, 30(6), 681-684.
- Brand, M., Laier, C., & Young, K. (2014). Internet addiction: coping styles, expectancies, and treatment implications. Front. Psychol, 5, 1256.
- Comscore. (2011). It’s a Social World: Top 10 Need-to-Knows About Social Networking and Where it’s Headed. http://www.comscore.com/Press_Events/Presentations_Whitepapers/ 2011/it_is_a_social_world_top_10_need-to-knows_about_social_networking
- Coutlee, C. G., Politzer, C. S., Hoyle, R. H., & Huettel, S. (2014). An abbreviated impulsiveness scale constructed through confirmatory factor analysis of the Barratt Impulsiveness Scale Version 11. Arch. Sci. Psychol, 2, 1-12.
- Craig, G. J., & Baucum, D. (2001). Human development. Prentice Hall.
- Davis, R. (2001). A cognitive-behavioral model of pathological Internet use. Comput. Human. Behav, 17, 187-195.
- Do, Y. K., Shin, E., Bautista, M., & Foo, K. (2013). The associations between self-reported sleep duration and adolescent health outcomes: what is the role of time spent on Internet use? Sleep Med, 14(2), 195-200.
- Dong, G., Lu, Q., Zhou, H., & Zhao, X. (2011). Precursor or sequela: pathological disorders in people with Internet addiction disorder. PLoS One, 6(2), e14703.
- Dontsov, A. I., & Perelygina, E. B. (2014). Humanities’ approaches to interpretation of criteria for singling out content exposing children to negative informational and psychological effects. Procedia – Social and Behavioral Sciences, 146, 134-140.
- Edmondson, A., & Mogelof, J. (2006). Explaining psychological safety in innovation teams: organizational culture, team dynamics, or personality? In L. Thompson & H.-S. Choi (Eds.), Creativity and Innovation in Organizational Teams (pp. 109-136). Erlbaum.
- Ellison, N. B., Steinfield, C. & Lampe, C. (2007). The benefits of facebook “friends:” social capital and college students’ use of online social network sites. J. Comput. Mediat. Commun, 12, 1143-1168.
- Green, L., Brady, D., Olafsson, K., Hartley, J., & Lumby, C. (2011). Risks and safety for Australian children on the internet. Cultural Science Journal, 4(1). https://doi.org/10.5334/csci.40
- Greenfield, P. & Yan, Z. (2006). Children, adolescents, and the Internet: A new field of inquiry in developmental psychology. Dev. Psychol, 42, 391-394.
- Ha, J., Kim, S. Y., Bae, S. C., Bae, S., Kim, H., & Cho, S. C. (2007). Depression and Internet addiction in adolescents. Psychopathology, 40, 424-430.
- Helson, R., & Wink, P. (1987). Two conceptions of maturity examined in the findings of a longitudinal study. Personality processes and individual differences. J. Pers. Soc. Psychol, 53, 531-541.
- Internet World Stats. (2017). Facebook Users in the World 2017. http://www.internetworldstats.com/facebook.htm
- John, O. P., & Srivastava, S. (1999). The Big-Five trait taxonomy: History, measurement, and theoretical perspectives. In L. A. Pervin & O. P. John (Eds.), Handbook of personality: Theory and research. Volume 2 (pp. 102-138). Guilford Press.
- Kim, J., LaRose, R. & Peng, W. (2009). Loneliness as the cause and the effect of problematic Internet use: the relationship between Internet use and psychological well-being. CyberPsychol. Behav, 12, 451-455.
- Kim, K., Ryu, E., Chon, M-Y., Yeun, E-J., Choi, S-Y., Seo, J-S., & Nam, B. W. (2006). Internet addiction in Korean adolescents and its relation to depression and suicidal ideation: A questionnaire survey. Int. J. Nurs. Stud, 43, 185-192.
- Kraut, R., Kiesler, S., Boneva, B., Cummings, J., & Helgeson, V. (2002). Internet paradox revisited. J. Soc. Issues, 58, 49-74.
- Kraut, R., Patterson, M., Lundmark, V., Kiesler, S., Mukopadhyay, T., & Scherlis, W. (1998). Internet paradox: a social technology that reduces social involvement and psychological well-being? Am. Psychol, 53, 1017-1031.
- Lam, L., Peng, Z., Mai, J., & Jing, J. (2009). Factors associated with Internet addiction among adolescents. CyberPsychol. Behav, 12(5), 551-555.
- Little, M., & Kobak, R. (2003). Emotional security with teachers and children’s stress reactivity: A comparison of special-education and regular-education classrooms. J. Clin. Child Adolesc. Psychol, 32, 127-138.
- Livingstone, S., & Haddon, L. (2009). EU Kids online. J. Psychol, 217, 236-239.
- Mitchell, P. (2000). Internet addiction: Genuine diagnosis or not? Lancet, 355, 632.
- Morahan-Martin, J., Alexander, C., & Mitchell, K. J. (1999). The relationship between loneliness and internet use and abuse. CyberPsychol. Behav, 2, 431-440.
- Morrison, C., & Gore, H. (2010). The relationship between excessive Internet use and depression: a questionnaire-based study of 1.319 young people and adults. Psychopathology, 43, 121-126.
- Paterson, M., Green, J. M., Basson, C., & Ross, F. (2002). Probability of assertive behavior, interpersonal anxiety and self-efficacy of South African registered dietitians. J. Hum. Nutr. Diet, 15, 9-17.
- Pratarelli, M., Browne, B., & Johnson, K. (1999). The bits and bytes of computer/Internet addiction: A factor analytic approach. Behav. Res. Methods Instrum. Comput, 31, 305-314.
- Rogers, C. R. (1959). A theory of therapy, personality, and interpersonal relationships: as developed in the client-centered framework. In S. Koch (Ed.), Psychology: A Study of a Science. Volume 3 (pp. 184-256). McGraw-Hill.
- Scheider, B. H., Atkinson, L., & Tardif, C. (2001). Child-parent attachment and children’s peer relations: A quantitative review. Dev. Psychol, 37, 86-100.
- Shapira, N., Goldsmith, T., Keck, P., Khosla, U., & McElroy, S. (2000). Psychiatric features of individuals with problematic Internet use. J. Affect. Disord, 57, 267-272.
- Shapira, N., Lessig, M., Goldsmith, T., Szabo, S., Lazoritz, M., Gold, M., & Stein, D. J. (2003). Problematic Internet use: proposed classification and diagnostic criteria. Depress Anxiety, 17, 207-216.
- Shmelyov, A. G. (2002). Psikhodiagnostika lichnostnykh chert [Psychodiagnostics of personal traits]. Rech’.
- Tegano, D. W. (1990). Relationship of tolerance of ambiguity and playfulness to creativity. Psychol. Rep, 66, 1047-1056.
- Tsitsika, A., Critselis, E., Louizou, A., Janikian, M., Freskou, A., & Kafetzis, D. A. (2011). Determinants of Internet addiction among adolescents: a case-control study. Sci. World J, 11, 866-874.
- Turel, O., He, Q., Xue, G., Xiao, L., & Bechara, A. (2014). Examination of neural systems sub-serving facebook “addiction”. Psychol. Rep, 115, 675-695.
- Turel, O., & Serenko, A. (2012). The benefits and dangers of enjoyment with social networking websites. Eur. J. Info. Systems, 21, 512-528.
- Uebelacker, S., & Quiel, S. (2014). The Social Engineering Personality Framework. In G. Lenzini & G. Bella (Eds.), Workshop on Socio-Technical Aspects in Security and Trust, Proceedings of 4th STAST 2014, Institute of Electrical and Electronics Engineers, Vienna, Austria, 18 July 2014 (pp. 24-30). IEEE.
- Urban, K. K. (2003). Toward a Componential Model of Creativity. In D. Ambrose, L. M. Cohen & A. J. Tannenbaum (Eds.), Creative Intelligence: Toward Theoretic Integration (pp. 81-112). Hampton Press Inc.
- Van der Mark, I. L., van Ibzendoorn, M. H., & Bakermans-Kranenburg, M. J. (2002). Development of empathy in girls during the second year of life: Associations with parenting, attachment, and temperament. Soc. Dev, 11, 451-468.
- Winnicott, D. W. (1960). Ego distortion in terms of true and false self. In D. W. Winnicott (Ed.), The Maturational Processes and the Facilitating Environment (pp. 140-152). Karnac Books.
- Yen, J-Y., Ko, C-H., Yen, C-F., Wu, H-Y., & Yang, M-J. (2007). The comorbid psychiatric symptoms of Internet addiction: attention deficit and hyperactivity disorder (ADHD), depression, social phobia, and hostility. J. Adolesc. Health, 41, 93-98.
- Yoo, H., Cho, S., Ha, J., Yune, S., Kim, S., & Lyoo, I. K. (2004). Attention deficit hyperactivity symptoms and Internet addiction. Psychiat. Clin. Neuros, 58, 487-494.
- Young, K. (1998). Internet addiction: The emergence of a new clinical disorder. CyberPsychology and Behavior, 1(3), 237-244.
- Zotova, O. Yu. (2012). Tekhnologii kommunikativnogo vzaimodeistviya dlya obespecheniya bezopasnosti i doveriya [Communicative interaction technologies for safety and trust]. National Psychological Journal, 1(7), 88-94.
- Zotova, O. Yu., & Zinchenko, Yu. P. (2014). Parents’ Notions of the Internet Information Aimed at Children. Procedia – Social and Behavioral Sciences, 146, 61-67.
Copyright information

This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International License.
About this article
Publication Date
15 November 2020
Article Doi
eBook ISBN
978-1-80296-093-8
Publisher
European Publisher
Volume
94
Print ISBN (optional)
-
Edition Number
1st Edition
Pages
1-890
Subjects
Psychology, personality, virtual, personality psychology, identity, virtual identity, digital space
Cite this article as:
Zotova, O. Y., Syutkina, E. N., & Solodukhina, O. S. (2020). Psychological Security Of Teenagers In The Web Space. In T. Martsinkovskaya, & V. Orestova (Eds.), Psychology of Personality: Real and Virtual Context, vol 94. European Proceedings of Social and Behavioural Sciences (pp. 871-880). European Publisher. https://doi.org/10.15405/epsbs.2020.11.02.105

